A Russia-linked cyber espionage group has been discovered using spyware disguised as documents from a Ukrainian military charity and Starlink satellite internet verification data to target Ukrainian organisations and NATO member states, according to cybersecurity researchers.
New DrillApp Backdoor Identified in Campaign
The operation, identified by cybersecurity firm Lab52, involves a backdoor known as DrillApp that provides attackers with extensive access to compromised systems. Once installed, the malicious software allows for the uploading and downloading of files, audio recording via microphones, and image capture from webcams. Researchers detected two versions of the spyware used in the campaign, differing primarily in the lures used to deceive victims.
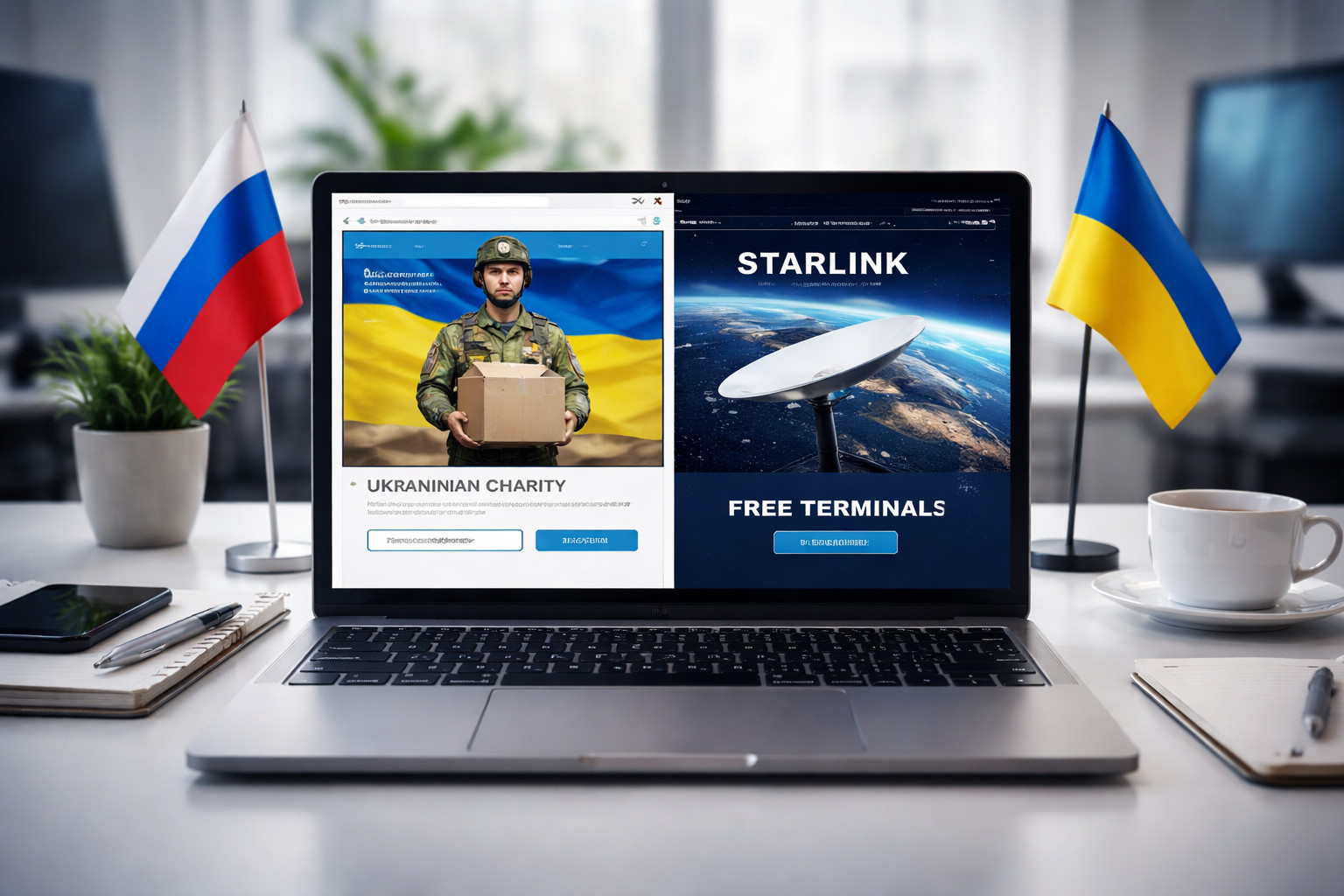
Charity and Starlink Verification Used as Deceptive Lures
Attackers distributed the malware using data that impersonated requests from the Ukrainian charity ‘Come Back Alive’, which provides support to the country’s armed forces. Additional lures involved information related to the verification of Starlink satellite internet terminals. Ukraine implemented a verification system for these terminals in early February after authorities confirmed Russian forces had begun installing the technology on strike drones.
Browser-Based Delivery Evades Security Measures
When the malicious file is opened through the Microsoft Edge browser, it enables attackers to access the victim’s file system and capture audio, video, and screen recordings. Cybersecurity experts note that using web browsers for delivery is particularly effective because browsers often have legitimate access to sensitive device functions like cameras and microphones, making malicious activity harder to detect. Antivirus tools also rarely flag browsers as suspicious.
Links to Russian Military Intelligence Apparatus
Researchers attribute the campaign to a hacking collective known as Laundry Bear, also identified as Void Blizzard, which has been active since at least 2024. Cybersecurity analysts have noted tactical similarities between this group’s operations and those of the Russian military intelligence unit APT28, widely known as Fancy Bear. Microsoft has previously reported that the group successfully penetrated organisations across several Ukrainian sectors, including education, transport, and defence.
Campaign Extends Beyond Ukrainian Borders
The cyber espionage activity is not confined to Ukraine. The group has previously targeted institutions in NATO member countries, indicating a broader operational remit. Ukraine’s Computer Emergency Response Team (CERT-UA) reported a separate operation by the same group targeting the country’s armed forces earlier this year, noting the use of similar techniques involving charity-themed lures and the placement of malicious components on public text-sharing services.
Early-Stage Malware Signals Evolving Threats
Lab52 assessed that the spyware appears to be in an early stage of development, suggesting the actors are experimenting with new methods to bypass security defences. The use of legitimate platforms and evolving lures underscores the continuous adaptation of state-sponsored cyber threats. The incident highlights the critical importance of information sharing between Ukrainian cyber defence units, Western researchers, and European security structures to identify such threats before they cause strategic damage.